Being an IT admins means that you have lots of responsibilities that play a key role in keeping your company going. Making sure that your environment is secure at all times is definitely among them.
In this article we are going to discuss some often forgotten aspects that you need to look at to ensure maximum security and minimize threats.
Enemy Within
Everybody knows that guarding your environment from outside threats is very important. There is absolutely no need in justifying this obvious point. Everybody does that and there are a lot of instruments that can help you. Those tools get better and better every day to keep up with growing threats. The thing is that many people just stop at that point. But they really shouldn’t.
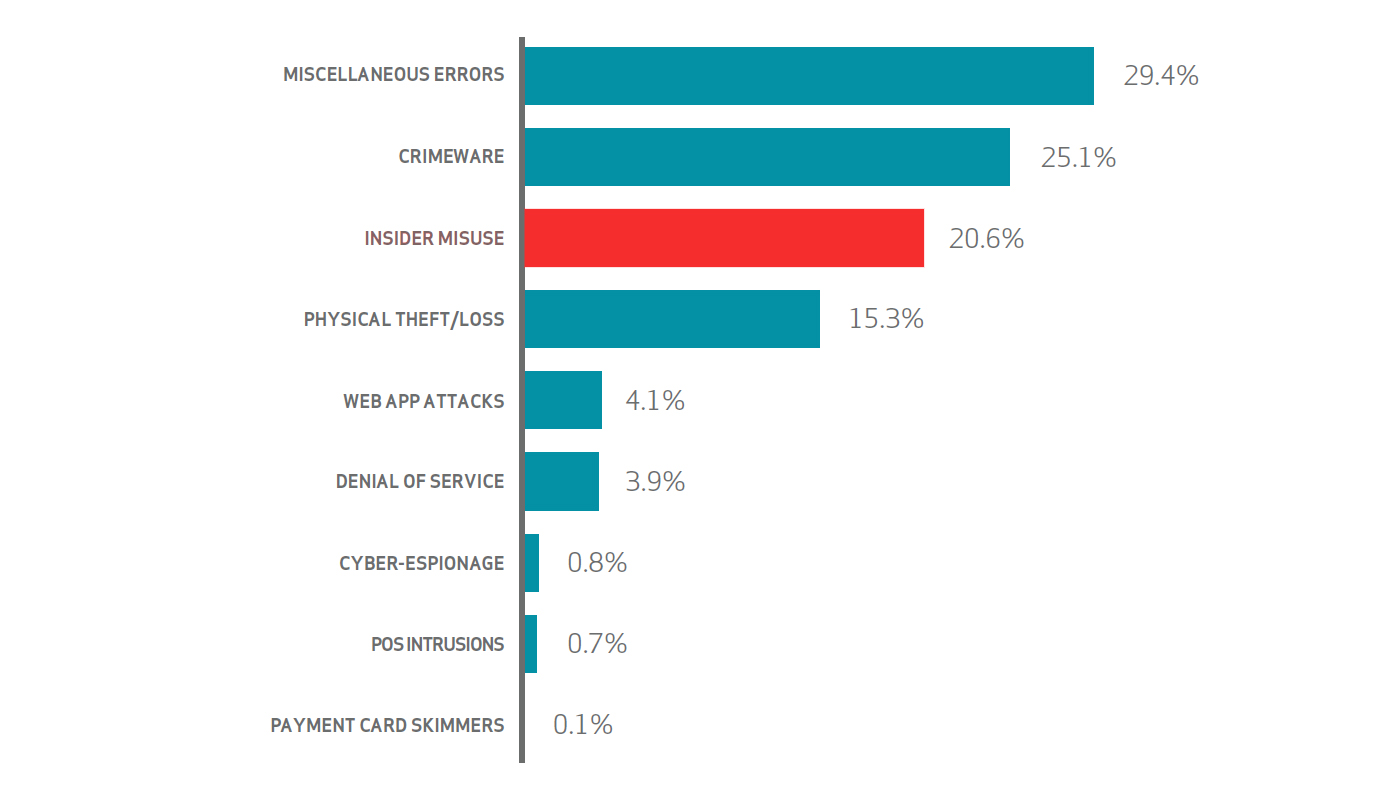
According to the 2015 Data Breach Investigation Report by Verizon, 20.6% of threats occur because of insider misuse, which is the third most popular cause of all security incidents. And the majority of those insider misuses are caused by abuse of permissions and privilege.
According to the same study, the time needed to discover such threats is constantly rising over the years, which makes the problem even worse.
What Can Help
So the logical question that should be arising in your head is “Can I do something about it here and now?”
Yes, you can! And Adaxes can help you with that.
Role-Based Access Control

First and foremost thing that you can do to keep permissions under control is to make sure that the mechanism of giving them out is working properly. For that purposes Adaxes features a Role-Based Access Control model.
Such approach ensures that once all roles are populated in the system, role-based privileges can be given out and updated quickly across your entire environment. If you need to apply any changes, there’s only one place you need to apply it to, so you can be sure that no privileges would be left hanging around after the changes occur.
AD Cleanup and Proper Deprovisioning

Stale user account and access rights of leaving employees are another big source of potential threat. But Adaxes can help you in eliminating them.
Firstly, with Adaxes you can automatically perform cleanup procedures such as removing unused user accounts, empty security groups, etc. Performing such operations on a regular basis is a simple but efficient way to keep your environment nice and tidy.
Secondly, Adaxes can automatically perform proper deprovisioning procedures that can not only disable users and move them to a specific OU, but also remove them from all groups, archive Exchange mailboxes, revoke Office 365 licenses, disable user for any other connected system — all that is done automatically and in one go. This means that the probability of having unwanted accounts and permissions due to improper deprovisioning tends to zero.
Approvals

Internal misuse is often caused by permission escalation. One of the reasons it can happen is lack of control over delegated tasks. But this will no longer be the case once Adaxes comes into play.
With Adaxes you can add an approval step to practically any operation. So higher level authorities can delegate more but at the same time retain control and prevent unwanted privilege escalations.
Reports and Notifications

As already said, time to discover security breaches is critical. With Adaxes this task can be a bit easier as admins have reports and notifications at their disposal for proper auditing.
Reports can be accessed via the Adaxes Web Interface and can be used to regularly monitor your environment. Adaxes also features notification which can be triggered by various events in AD, so that admins can always be up to date with what’s going on. E.g. they can be sent once users are deleted in AD or when new users are added to certain security groups. Such notifications can be sent either by email and/or SMS.
Conclusion
Security is and will always be a major concern for ant admin working in any IT environment. So it is really important to remember that apart from working on advanced protection from outside threats, there are still simple things that can be done internally to keep you out of trouble.
