Creating an initial password for newly hired employees is an important part of user provisioning. Despite it being only a one-time procedure, it's not as simple as it sounds. In fact, doing it wrong can cause a lot of security problems. So, let's find out, how to do it properly.
Creating a Password

First, you need to create a password for the new user. Obviously, the ‘user must change password at next logon’ option must be enabled. But before that you need to decide, what the initial password will be. Here are a few options.
Pa$$word
Some companies take a simple, yet very insecure path. They use the same standard password for all new users, e.g. Pa$$word. This is a terrible practice that must be abandoned ASAP for obvious reasons.
If everybody knows the initial password of any new user, there's always a risk that someone can gain access to it and abuse your system in all sorts of ways. This is especially dangerous if accounts are created some time in advance before new users start working. Thus, all that time their accounts are exposed.
Standard Expression
Using patterns for new passwords is a slightly better approach. It can be based on some personal information that is passed to HR during the hiring process, e.g. 'Name' + 'Hiring date'. So, for James May, who's hired on the 8th of August 2017 a password would be James08082017.
It's much better than having the same password for everyone, but the problem with it is still the same. Anybody who is familiar with how the system works can guess it. Again, not very good in terms of security.
Random Passwords
The best and most secure way to do that is to generate a completely random password for every new user. This way you can be sure that nobody will be able to guess and therefore inappropriately use the password, neither from the inside, nor from the outside.
Communicating the Password
So, you've created the password, but it's still not the end of the story. The next thing to do is to pass the it to the user, so it can be used for the first logon. Let's have a look at the options you have.
Pen and Paper
Despite having all sorts of wonderful technology at their disposal, a lot of IT environments still use pens and papers. Even if a proper random password was generated, it's still written down and passed to the new hire.
Writing passwords down is always a bad idea. Anyone can intercept it on the way. And from a security perspective, if something can go wrong, you must assume it inevitably will. Having a healthy paranoia is very useful here.
Managers
Another widely used way to pass the password to the user, is to send it to their managers, e.g. by email. The last mile (manager-user communication) can still use the pen and paper method, but at least they are usually in the same office or at least closer to each other that to the IT department, which decreases the risks slightly.
However, you still need to trust the manager to keep the password safe. And you should also consider that if you are scaling this approach to the entire system, you are assigning yourself to trust any manager. Are you sure you want to do that?
SMS or Personal Email
The best way to conduct the initial password communication to the user is to eliminate the human factor completely. This is actually possible and you have all the necessary information for that.
You can send the randomly generated password to the user either by email or SMS. This means you avoid any other agents in-between, making things as secure as possible. Of course, to do that you’ll need to introduce some sort of automation to the process. Nobody will ever type in passwords using phones to send an SMS. The ideal case is when the password is generated and then automatically sent to the user with no human interaction at all.
Automation
So now the method of communicating initial passwords is the following:
- a new user account is created;
- a random password is generated;
- the password is automatically sent to the user via SMS or email;
- the user changes the password at first logon.
That’s all convenient and secure, but there is still one more step further that you can take. This whole procedure can be made a part of automated user onboarding. This means that it will be run instantly after any user account is created in AD along with the other operations, such as creating an Exchange mailbox or adding the user to all necessary groups.
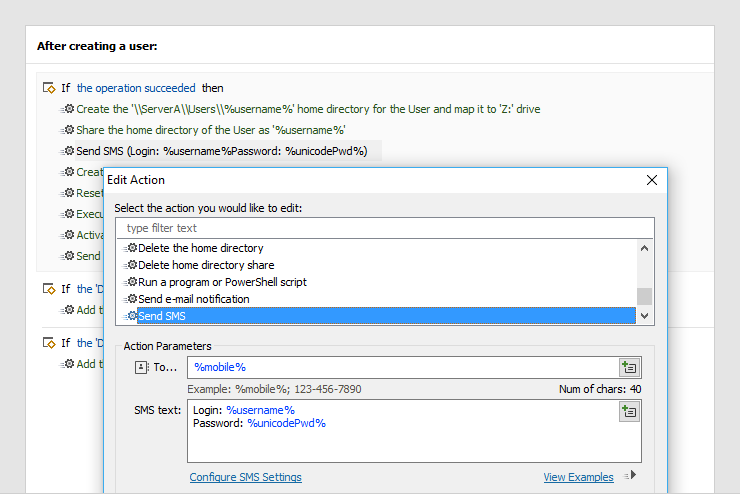
With Adaxes that’s just adding two lines to your list of provisioning actions. First you need to generate a random password using a built-in action, and then add send it to the user. In addition, you can customize the message you are sending to carry a logon name or any other additional information that’s relevant to the user.
Using Adaxes Web Interface for onboarding also allows you to completely hide the password field from your provisioning forms. This means that the only person who can possibly ever see the initial password, is the user it’s sent to.
By implementing proper automation, you can make sure that you use the right method of communicating passwords to new users, but also know that it’s properly executed every single time with no missed steps or other mistakes.
Enjoy. And keep your passwords safe.
