Microsoft's Active Directory has been around for a very long time, since its debut as part of Windows Server 2000. Since those early days, there have been plenty of changes, improvements and schema updates to improve the platform which has become so popular, and a key component of most Windows based environments. However, there hasn't been much of a focus on ways to clean up the Organizational Units (OUs) and objects inside them; that is left up to you to do for yourself.
Adaxes blog
If you're a Windows Systems Administrator, then you've probably had to manage Active Directory Users and Computers. To the uninitiated, it can seem simple - it's just a bunch of computers and users in a folder-like structure known as Organizational Units (OUs). However, understanding the hows and whys of designing the structure in certain ways to meet your company needs is an important consideration. If it's not done right from the start, it can be a project in itself to unravel the resulting mess to bring it all back to a manageable state.
In the first part of this series, I talked about the importance of automation, and simplification of automation, for the systems administrator of 2018. Adopting technologies that can automate common, labour-intensive tasks but do not contribute to a huge increase in complexity is, I believe, vital. By allowing administrators to quickly and easily configure processes that reliably perform manual tasks, you remove both the overhead of time to create them and the potential for human error.
I see a lot of buzz in the industry about IoT (Internet of Things), Artificial Intelligence, Augmented Reality, blockchain and voice activation. But these are all technologies that require a substantial amount of investment, evangelization, and a defined “jump” to a newer way of working. Whilst they may be able to provide excellent services in the future, they are still very much at an embryonic stage when it comes to enterprise adoption.
On-premises Microsoft Exchange supports three types of Active Directory groups – security groups, distribution groups and dynamic distribution groups. Each group has its own purpose and limitations, so which group should you use when?
The year 2018 is here and you probably already have your New Year’s resolutions. Eating healthier food, going to the gym, learning a new foreign language, all these things are most probably present on your list. These are personal goals and promises, but what about the professional ones?
Being left obsolete due to incoming power of automation is a common fear among the IT pros community. Especially with all the media stories about the rise of neural networks and AI that pop up almost every day, it’s really tempting to jump on the hype train and start the panic. So, will all the admin jobs eventually be taken by robots?
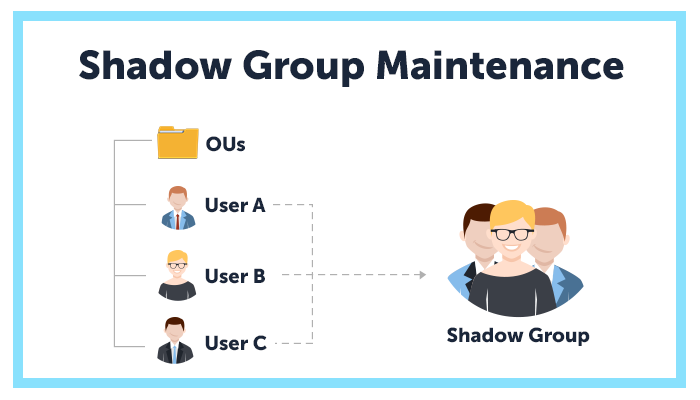
In one of our previous articles we discussed automating group membership management. But there is a specific type of groups that deserves a bit more attention. Shadow groups.
Users often take their domain-joined laptops away from company’s premises. They can go on a business trip or just take a computer home to finish some work over the weekend. However, if they forget their password, they get locked away completely, which can become a real problem. Even if they can get to the help desk and get their password reset, they still need to wait until they come back and connect to the company’s network to be able to log in.
Managing an AD environment in an educational institution is in many ways similar to any other IT shop, but with some specific challengers on top. For example, in addition to the everyday routine, that can be quite complex by itself, IT departments in schools and universities get those super intense periods of extra load, when new students come in and the old ones leave. Solving such situations with manual management is extremely inefficient, leaving a lot of headroom for improvement.