Hello,
I've got a problem with Windows Authentication in web interface.
When I am in Form Authentication, there is no problem.
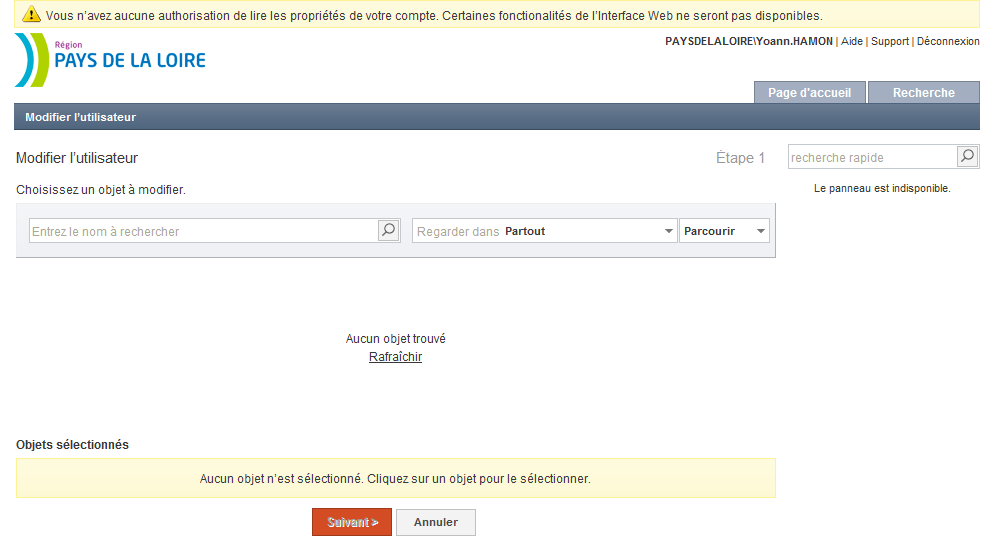
If I change for Windows Authentication, I am correctly identified and logged but after that, I don't have any permission on AD, even to read.
Screenshots will be better than my english...
Thanks for your help
Yoann HAMON
Windows authentication :
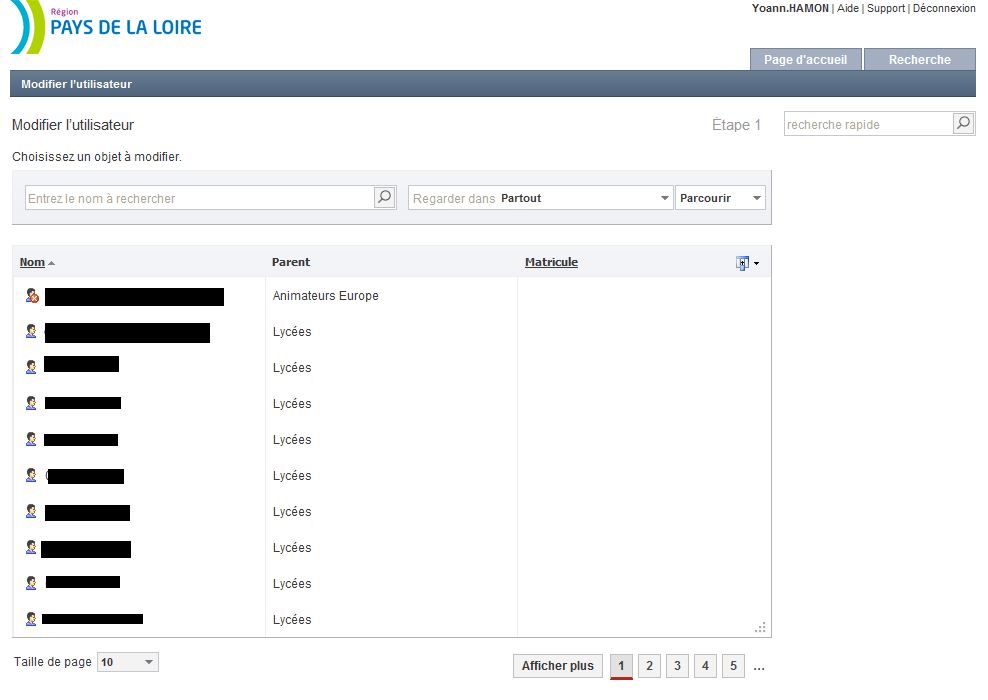
Form authentication :