Configure sign in settings
In this tutorial you will learn how to customize the Common Sign In page for Adaxes Web interface, configure logon options (SAML-based single sign-on, integrated Windows authentication), modify brute force protection settings, and other options related to sign-in.
Common Sign In
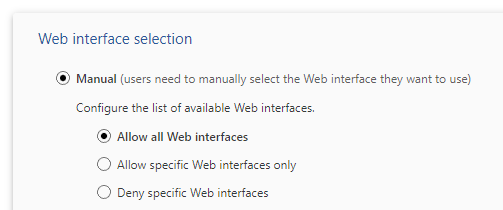
Adaxes Web interface provides a common sign-in page that enables users to log in to different Web interfaces from a single place. The feature can be configured to either allow users to manually select the Web interface they want to use, or automatically redirect them to a specific Web interface based on the rules you define.
By default, the Common Sign In page allows users to select themselves the Web interface they want to log in to. You can configure which Web interfaces are available for selection and specify the Web interface to be selected by default.
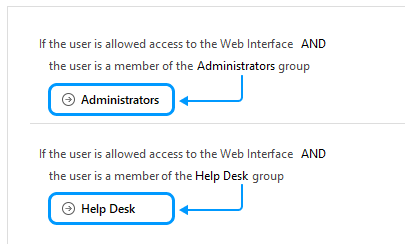
Alternatively you can enable automatic selection of Web interfaces. When enabled, users will be unable to select a Web interface, and will instead get automatically redirected based on if/else rules. For example, if a user is a member of the Administrators group, they can be automatically redirected to the Administrator Web interface.
How to configure Web interface selection settings {id=selectionsettings}
-
Open Adaxes Web interface configurator.
-
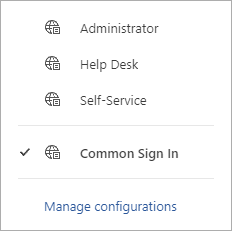
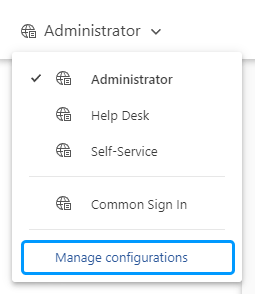
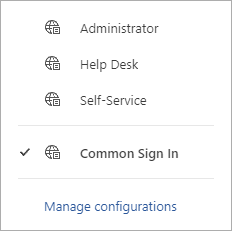
In the drop-down list located in the top left corner, click Common Sign In.
-
Configure the settings in the Web interface selection section.
-
Save the changes.
If you don't want the Common Sign In page to be available to users, you can disable the feature.
How to disable Common Sign In {id=disablecommonsignin}
-
Open Adaxes Web interface configurator.
-
In the drop-down list located in the top left corner, click Manage Configurations.
-
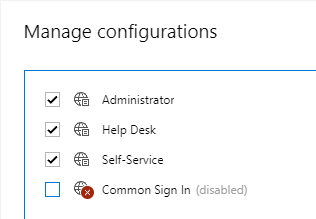
In the dialog that opens, clear the checkbox for Common Sign In.
-
Click OK and save the changes.
Sign in settings
In this part of the tutorial you will learn how to:
-
Enable two-factor authentication for the Username/Password form authentication.
-
Enable automatic logon or SAML-based single sign-on for the Web interface.
-
Customize brute force protection settings.
-
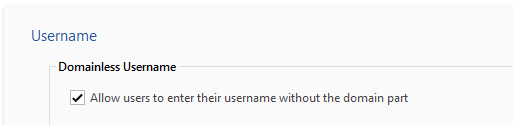
Allow users to enter their usernames without the domain part when logging in to the Web interface. Example: jsmith instead of jsmith@example.com.
-
Allow users to specify a certain property value of their account as login name. For example, you can allow users to specify their email address or Employee ID.
-
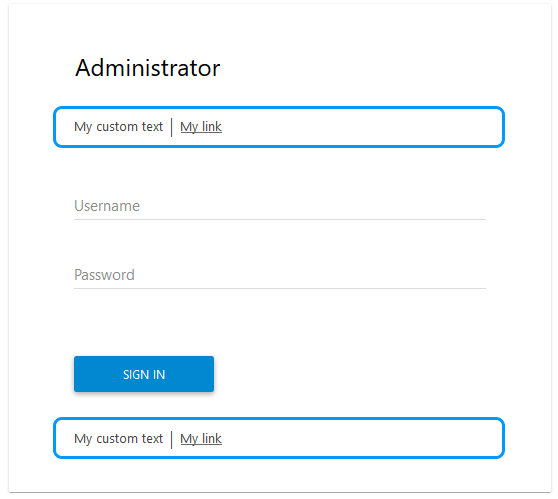
Embed custom HTML code into the Sign In page.
To configure options related to the Sign In page of the Web interface:
-
Open Adaxes Web interface configurator.
How
-
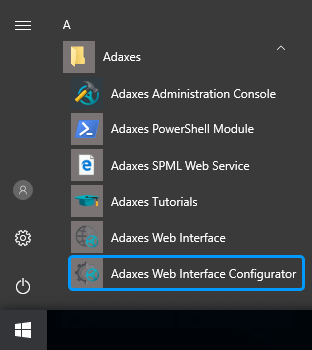
On the computer where Web interface configurator is installed, open Windows Start menu.
-
Click Adaxes Web Interface Configurator.
To configure the Web interface, you need to have the appropriate permissions.
Permissions
The permissions to configure the Web interface are delegated via security roles. By default, only service administrators have the appropriate permissions. To enable other users to configure the Web interface, grant them the corresponding permissions.
To create a security role that grants the permissions to configure Web interface:
-
In Adaxes Administration console, right-click your Adaxes service, point to New and click Security Role.
-
Enter a name for the new security role and click Next.
-
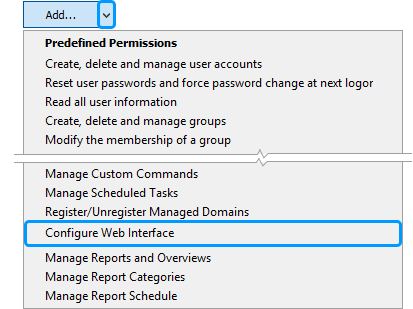
On the Permissions step, click the down arrow embedded into the Add button and click Configure Web Interface.
-
Click Next and follow the steps in the wizard.
-
-
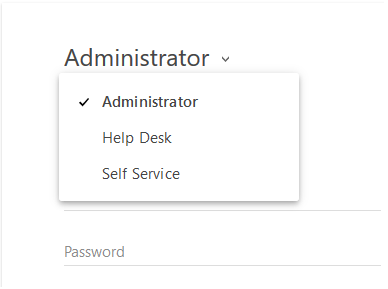
In the top left corner, select the Web interface you want to customize.
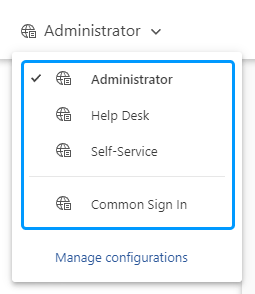
By default, all Web interfaces use the Sign In settings of the Common Sign In page. If you want a particular Web interface to have different settings, select it in the list. Otherwise, select Common Sign In.
-
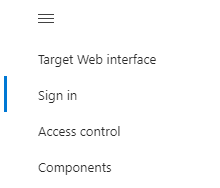
In the left navigation menu, click Sign in.
-
To enable two-factor authentication:
-
Select Username/password form authentication.
-
Select Enable two-factor authentication.
-
Select the authenticator app you want to use.
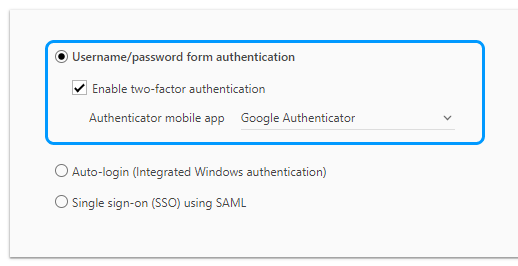
After two-factor authentication is enabled, users will need to install the app on their device and activate it upon the first login to the Web interface. During subsequent logins, they will be prompted to enter a code generated by the app to sign in.
View how it works {id=how2faworks}
If a user loses their mobile device or gets a new one, they will need to re-activate the authenticator app on the new device. For details on how to do it, see Reset authenticator app.
-
-
To enable single sign-on for the Web interface you can use either Integrated Windows authentication or SAML authentication.
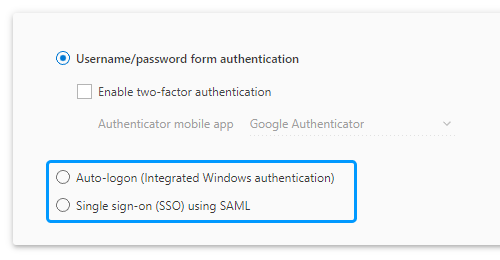
Auto-logon (Integrated Windows authentication)
If automatic logon is enabled, users will not need to enter their username and password to sign in, and the Web interface will use Kerberos/NTLM for authentication. It means that all users will be signed in with the same account specified during log in to Windows.
Single sign-on (SSO) using SAML
If SAML authentication is enabled, the Web interface will send a request to an external identity provider (Okta, OneLogin, Microsoft Entra ID, etc.) to authenticate the user. If a user is already authenticated against the provider, they will be automatically logged in to the Web interface without any authentication process. For details on how to configure SAML authentication settings, see Enable SAML-based single sign-on.
-
To enable protection against brute force attacks, select the Brute force protection option.
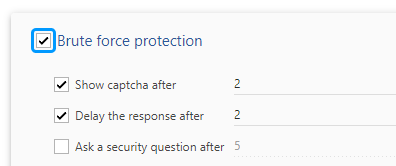
For details on how to configure brute force protection, see Prevent brute force attacks.
-
In the Username section, configure settings related to the Username field.
-
In the Page customization section, you can customize the top and bottom parts of the Sign In page.
-
Save the changes.

